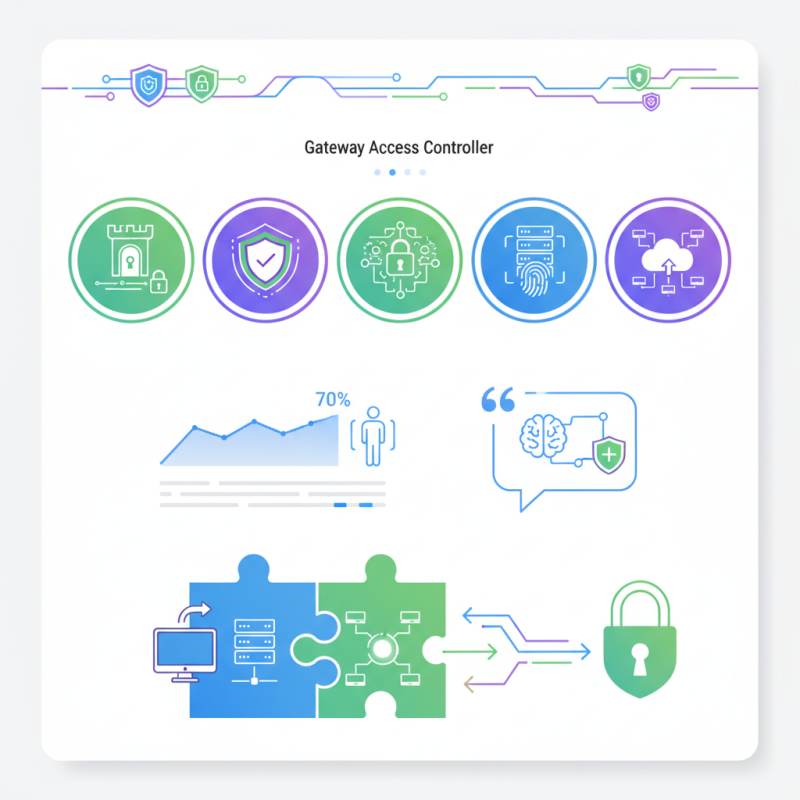
In today's digital landscape, Gateway Access Controllers play a crucial role in ensuring secure and efficient network access. According to a recent industry report by Cybersecurity Insights, over 70% of organizations struggle with unauthorized access issues. This places Gateway Access Controllers in a vital position. Experts like Dr. Emily Chang emphasize their importance by stating, “Effective control of access points is essential for robust network security.”
Many companies are shifting their focus towards implementing advanced Gateway Access Controllers. This shift is driven by the need for better security protocols and user management. Yet, achieving this can be challenging. Organizations often struggle to integrate new technologies with existing systems, leading to potential vulnerabilities. These complexities need addressing to optimize network protection.
Exploring the top Gateway Access Controllers helps identify which solutions meet current needs. The market offers a variety of options, each with strengths and weaknesses. This evolving landscape invites critical evaluation. Understanding these tools not only aids in secure access but also highlights areas for improvement in network defense strategies.
Gateway Access Controllers (GACs) play a key role in network security. They manage traffic between internal networks and external connections. Recent reports indicate that 61% of organizations suffered a data breach in the past year. This emphasizes the need for robust security measures.
Implementing GACs helps reduce unauthorized access. They enforce rules and monitor traffic flow. Features like multi-factor authentication can deter intruders. A study highlights that 66% of companies using effective access controls reported fewer security incidents.
Yet, challenges remain. Some organizations struggle with integrating GACs into existing systems. Proper configuration is crucial. Missteps can lead to vulnerabilities. It’s essential to invest in training and resources. Balancing security and accessibility is not easy, but it is necessary.
When choosing gateway access controllers, features matter. Look for robust security protocols that protect sensitive data. Encryption capabilities are essential. They ensure data transmitted between the controller and devices remains safe. Multi-factor authentication adds an extra layer of security, preventing unauthorized access.
Consider user management capabilities as well. The ability to assign different access levels helps in maintaining control. Easy integration with existing systems is a must. It should fit seamlessly into your current infrastructure. This saves time and resources during setup.
Tips: Always assess the interface. A user-friendly design promotes efficiency. Do not overlook customer support services. Reliable support can resolve issues quickly, minimizing downtime. Regular software updates keep the system secure against new threats. Remember, not every controller will meet your needs. Reflect on what features are truly essential for your environment.
When it comes to gateway access controllers,
performance is key. They act as
security checkpoints for network traffic. Many organizations are seeking solutions
that balance efficiency with robust security features. But not all
controllers perform equally. Some struggle under high data loads, leading to delays.
Others may lack flexibility, making integration with existing systems a hassle.
Assessing various models reveals mixed results. Some excel in speed but fall short
in user management functionalities. Others prioritize security but add latencies in
their processes. Real-world applications often expose these flaws. Users frequently
find themselves questioning if they chose the right solution. It's essential to
evaluate specific needs against the unique strengths of each access controller.
Industry trends suggest a shift towards adaptable solutions. These offer
scalability and better performance under
strain. However, the market is filled with options, making selection challenging.
Users need to reflect on their current infrastructure and future requirements.
Without thoughtful consideration, organizations may face compromised security or
performance issues. Understanding your specific needs is crucial in this
evolving landscape.
As organizations seek improved security measures, gateway access controllers have gained traction. Industry statistics show a rise in adoption rates. Many companies are now prioritizing these systems for enhanced access control. The benefits are clear: increased security, streamlined operations, and better data management.
Data suggests that over 60% of businesses report higher security postures after implementing such systems. Streamlined authentication processes have proven crucial for large enterprises. These systems often reduce the risk of unauthorized access. However, adoption is not without challenges. Some companies struggle with integration into existing infrastructure. Also, the costs associated can be a barrier for smaller organizations.
Many decision-makers reflect on the need for proper training and support. While the systems themselves are beneficial, human factors remain a concern. Employees might find new systems complicated. Continuous training and feedback loops can help address these issues. Still, the benefits of reduced security breaches and improved efficiency seem worth the effort.
As the demand for security and access control surges, gateway access controllers are evolving rapidly. Market research reports predict significant growth. By 2025, the global market could reach $6.5 billion, reflecting a compound annual growth rate of around 9.2%. This evolution is driven by the integration of advanced technologies like AI and machine learning. These innovations enhance user authentication processes, making them smarter and more efficient.
However, not all trends are without challenges. Many systems struggle with interoperability. Businesses often find it hard to integrate newer models with existing infrastructure. In 2022, over 40% of organizations reported issues with compatibility between devices. Data security remains a critical point of concern. With cyber threats growing, companies must ensure that access controllers are robust against breaches.
The focus is also shifting towards user experience. While security is paramount, convenience cannot be overlooked. Businesses increasingly seek solutions that simplify access without compromising safety. Effective deployment of multi-factor authentication can ease user friction. Striking the right balance is essential for future growth in this sector.
| Controller Model | Key Features | Supported Protocols | Market Growth (%) | Future Trends |
|---|---|---|---|---|
| Model A | High Availability, Scalability | SSL, IPsec, L2TP | 15% | AI Integration, Enhanced Security |
| Model B | User Management, Multi-Factor Authentication | RADIUS, TACACS+, LDAP | 20% | Cloud Services, IoT Connectivity |
| Model C | Real-Time Monitoring, Easy Deployment | SNMP, SAML, OAuth | 25% | Advanced Analytics, Predictive Maintenance |
| Model D | Zero Trust Security, High Throughput | HTTPs, FTP, SSH | 30% | Decentralized Architecture, Edge Computing |
| Model E | Interoperability, Automation | MQTT, CoAP, WebSocket | 40% | Integration with AI and Machine Learning |
ccess Controllers (GACs)?
Implementing GACs can significantly lower the chances of data breaches. Studies show that many companies report fewer incidents after using them.
Integration with existing systems is often difficult. Misconfiguration can create vulnerabilities, making proper configuration essential.
Features like multi-factor authentication are crucial. They provide an extra layer of security against potential intruders.
Not all GACs perform the same. Some excel under high traffic, while others may create delays or lack flexible integration.
Employees may find new systems complicated. Ongoing training is necessary to ensure effective use and minimize human errors.
Reflect on specific infrastructure and future requirements. Consider current challenges to find the best solutions for security and performance.
GACs lead to increased security, better data management, and streamlined operations. Many companies report heightened security postures after implementation.
Yes, smaller organizations often struggle with the costs associated with implementing GACs. Budget considerations can hinder adoption.
Decision-makers often realize the importance of training and support. Human factors can impact the effectiveness of these systems despite their benefits.
Gateway Access Controllers play a crucial role in enhancing network security by managing access to the network and protecting against unauthorized intrusions. In this article, we explore the importance of these controllers, highlight key features that make them effective, and present a comparison of the top five Gateway Access Controllers based on their performance and capabilities. Understanding these features is essential for organizations aiming to strengthen their security posture while ensuring seamless user access.
Furthermore, we delve into industry statistics that reveal adoption rates and the benefits associated with implementing Gateway Access Controllers. As technology evolves, we also examine future trends and market growth that indicate an increasing reliance on these solutions. With the ever-growing complexity of cyber threats, investing in quality Gateway Access Controllers is becoming more essential for organizations seeking to safeguard their networks.

 Orix Steel
Orix Steel